🧠 Cisco ACI Demystified: “Treat as Virtual IP
Address” vs “Make this IP Address Primary”
In the world of Cisco
ACI, Bridge Domains (BDs) are the backbone of Layer 2 networking. But when
configuring subnets within a BD, two deceptively similar options often confuse
engineers:
- ✅ Make
this IP Address Primary
- 🌐 Treat as Virtual IP Address
Let’s break down what
each of these means, when to use them, and how they impact your ACI fabric.
🔹 What is “Make this IP Address Primary”?
This option is used to
define the default gateway for endpoints within the Bridge Domain.
✅ Key Characteristics:
- Only one primary IP per BD.
- Used for routing traffic between
subnets or to external networks.
- Responds to ARP requests from
endpoints.
- Can be advertised externally if
route advertisement is enabled.
📌 When to Use:
- In single-site ACI deployments.
- When you want the fabric to act as
the default gateway for endpoints.
- For standard BD configurations where no
multi-site or stretched fabric is involved.
🔹 What is “Treat as Virtual IP Address”?
This option is
designed for multi-site or stretched fabric deployments
where you want a consistent gateway IP and MAC address across
multiple locations.
🌐 Key Characteristics:
- Requires a Virtual MAC address.
- Enables Common Pervasive Gateway
(CPG) functionality.
- Ensures seamless endpoint mobility across
sites.
- Can coexist with a primary IP in
the same BD.
📌 When to Use:
- In multi-pod or multi-site ACI
environments.
- When you need Layer 3 gateway
consistency across data centers.
- For active-active data center
designs.
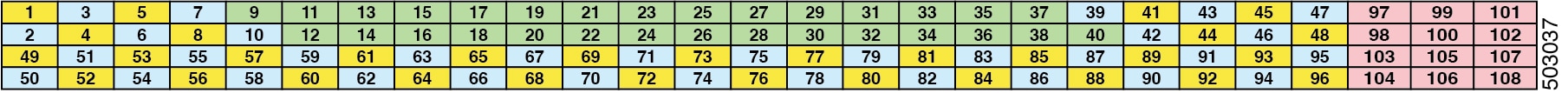
🔁 Side-by-Side Comparison
|
Feature |
Make this IP Primary |
Treat as Virtual IP Address |
|
Default Gateway Role |
✅ Yes |
✅ Yes (in multi-site) |
|
Number per BD |
One |
Multiple (with
virtual MAC) |
|
Requires Virtual MAC |
❌ No |
✅ Yes |
|
Use Case |
Single-site routing |
Multi-site gateway
consistency |
|
Supports Endpoint
Mobility |
❌ Limited |
✅ Seamless |
|
Route Advertisement |
✅ Yes (if enabled) |
✅ Yes (if enabled) |
🧪 Real-World Example
Imagine you have two
data centers—DC1 and DC2—connected via ACI Multi-Site. You want VMs
to move between them without changing their default gateway.
- You’d configure the same subnet in
both sites.
- Use “Treat as Virtual IP Address” with
a shared virtual MAC.
- This ensures the gateway IP and MAC
remain consistent, avoiding disruptions.
🧩 Final Thoughts
Both options serve
critical but distinct purposes. Choosing the right one depends on your ACI
topology and traffic flow requirements. For most single-site
deployments, “Make this IP Address Primary” is sufficient. But for
advanced, distributed environments, “Treat as Virtual IP Address” is
your go-to for seamless mobility and high availability.